EnvWatch: Find Exposed Cloud Secrets Before Hackers Do
There’s a quiet risk that creeps into every developer’s workflow; not flashy, not obvious, but persistent. It’s the slow accumulation of secrets: API keys copied during testing, forgotten .env files, SSH keys scattered across directories, AWS credentials still valid but long ignored. None of it feels urgent in the moment. Collectively, it creates an attack surface that’s hard to reason about.
The 2024 AWS .env Extortion Campaign
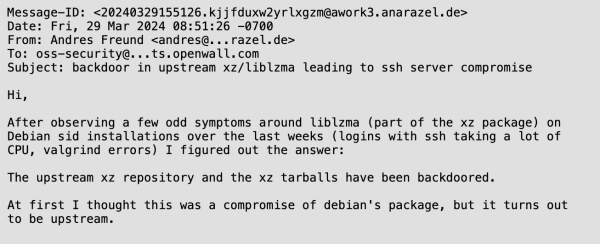
In 2024, Palo Alto Networks’ Unit 42 uncovered a large-scale extortion campaign built entirely around one thing: exposed .env files. Attackers ran automated scans across 230 million unique targets, harvesting credentials stored in publicly accessible environment files. The haul included 1,185 AWS access keys, 333 PayPal OAuth tokens, 235 GitHub tokens, and dozens of Slack webhooks and DigitalOcean tokens all extracted from files that developers had left reachable on misconfigured web servers.
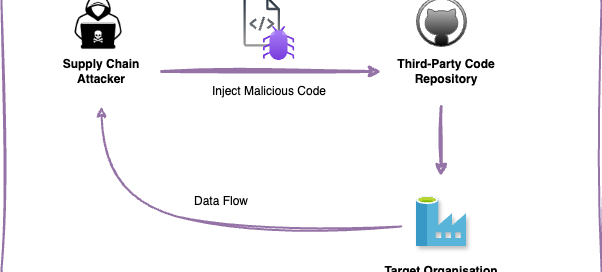
Once inside a victim’s AWS environment, attackers escalated privileges by creating new IAM roles with administrator permissions, then spun up Lambda functions to automate further scanning turning each victim’s own infrastructure into attack infrastructure for the next wave.
No sophisticated exploit. Three compounding failures: secrets stored in .env files, those files publicly accessible, and long-lived credentials with no rotation policy.
EnvWatch was built to address exactly that. It’s a lightweight Go utility that scans your system for exposed cloud secrets fast, local, and deliberately simple
The Problem: Secret Sprawl Is Inevitable
If